security in bluetooth rfid and wireless sensor networks In this paper, an overview of security issues like attacks and its countermeasures for wireless personal area networks such as Bluetooth, RFID and wireless sensor networks has been provided. 2012 AFC Wild Card Game: Cincinnati Bengals CIN 13 @ Houston Texans HOU 19: 01/05/13: 2012 NFC Wild Card Game: Minnesota Vikings MIN 10 @ Green Bay Packers GB 24: .
0 · Security in Bluetooth, RFID and wireless sensor networks
50 Pieces NFC Tags NFC Cards NTAG215 Blank Printable NFC Card ISO Size PVC Cards NFC Chip, Compatible with iPhone TagMo and All NFC Enabled Device. 672. $1795 ($0.36/Count) .
In this paper, an overview of security issues like attacks and its countermeasures for wireless personal area networks such as Bluetooth, RFID and wireless sensor networks has been provided. In this paper, an overview of security issues like attacks and its countermeasures .In this paper, an overview of security issues like attacks and its countermeasures for wireless . In this paper, an overview of security issues like attacks and its countermeasures for wireless personal area networks such as Bluetooth, RFID and wireless sensor networks has been provided.
In this paper, an overview of security issues like attacks and its countermeasures for wireless personal area networks such as Bluetooth, RFID and wireless sensor networks has been.
In this paper, an overview of security issues like attacks and its countermeasures for wireless personal area networks such as Bluetooth, RFID and wireless sensor networks has been provided.
In this paper, an overview of security issues like attacks and its countermeasures for wireless personal area networks such as Bluetooth, RFID and wireless sensor networks has been provided. Categories and Subject Descriptors C.2.0 [Computer-Communication Networks]: General— Security and protection. Wireless sensor network security is provided on two levels. 16 On the first level, encryption methods and firewalls are utilised to protect the network from outside attackers. Intrusion detection systems (IDS) are employed to defend against internal intruders at .
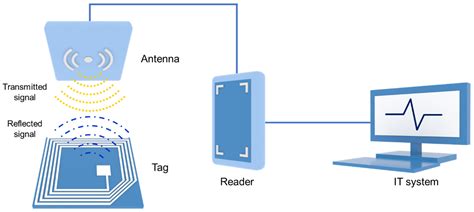
The inclusion of wireless communication technology also incurs various types of security threats. The intent of this paper is to investigate the security related issues and challenges in wireless sensor networks. We identify the security threats, review proposed security mechanisms for wireless sensor networks.This paper highlights the security related issues and challenges in communication networks. We also present the holistic view for the underlaying physical layer including physical infrastructure attacks, jamming, interception, and eavesdropping. In the past several years, there has been an increasing trend in the use of Radio Frequency Identification (RFID) and Wireless Sensor Networks (WSNs) as well as in the integration of both systems due to their complementary nature, flexible combination, and the demand for ubiquitous computing.
In this paper, we analyze the security criteria, internal and external security threats and attacks that can be done, and the mechanism used in the Wireless Sensor Network to address such. This publication provides information on the security capabilities of Bluetooth and gives recommendations to organizations employing Bluetooth wireless technologies on securing them effectively. In this paper, an overview of security issues like attacks and its countermeasures for wireless personal area networks such as Bluetooth, RFID and wireless sensor networks has been provided. In this paper, an overview of security issues like attacks and its countermeasures for wireless personal area networks such as Bluetooth, RFID and wireless sensor networks has been.
In this paper, an overview of security issues like attacks and its countermeasures for wireless personal area networks such as Bluetooth, RFID and wireless sensor networks has been provided.In this paper, an overview of security issues like attacks and its countermeasures for wireless personal area networks such as Bluetooth, RFID and wireless sensor networks has been provided. Categories and Subject Descriptors C.2.0 [Computer-Communication Networks]: General— Security and protection.
Wireless sensor network security is provided on two levels. 16 On the first level, encryption methods and firewalls are utilised to protect the network from outside attackers. Intrusion detection systems (IDS) are employed to defend against internal intruders at .
The inclusion of wireless communication technology also incurs various types of security threats. The intent of this paper is to investigate the security related issues and challenges in wireless sensor networks. We identify the security threats, review proposed security mechanisms for wireless sensor networks.
This paper highlights the security related issues and challenges in communication networks. We also present the holistic view for the underlaying physical layer including physical infrastructure attacks, jamming, interception, and eavesdropping. In the past several years, there has been an increasing trend in the use of Radio Frequency Identification (RFID) and Wireless Sensor Networks (WSNs) as well as in the integration of both systems due to their complementary nature, flexible combination, and the demand for ubiquitous computing.
datascan rfid reader
In this paper, we analyze the security criteria, internal and external security threats and attacks that can be done, and the mechanism used in the Wireless Sensor Network to address such.
Security in Bluetooth, RFID and wireless sensor networks
custom pvc rfid blocking card
custom rfid jewelry label
credit card rfid trackable
custom rfid apparel tag
Green Bay Packers 6-3 (third place, NFC North): The Packers, after a Week 10 bye, need to get back on track to strengthen their wild-card position by beating the Bears in .
security in bluetooth rfid and wireless sensor networks|Security in Bluetooth, RFID and wireless sensor networks