rfid credit card hacking One of the biggest public fears surrounding RFID hacking is with credit and debit cards. While your RFID card is safe in your wallet, a hacker scans the card in your pocket without you knowing. The attacker can then siphon money or steal information without you knowing about it. The Crimson Tide Sports Network represents one of the biggest and most-listened to college sports network in the South (and the nation) See a full listing of all the Alabama radio stations below. City. Call Sign. Frequency. Anniston. .
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hacking tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid scanning
$69.00
rfid scammers
Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here!
One of the biggest public fears surrounding RFID hacking is with credit and debit cards. While your RFID card is safe in your wallet, a hacker scans the card in your pocket without you knowing. The attacker can then siphon money or steal information without you knowing about it.
how to use an arduino to read rfid information
The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and Indala.With the recent shift to contactless payment cards, more cybercriminals are turning to RFID credit card theft via scanning. This article will explain how this theft happens and provide tips on how to protect your RFID credit card from potential thefts and other common payment card frauds. Despite demonstrations to show it's possible, documented cases of RFID credit card fraud are unknown. And as security professionals know, there is a huge gulf between potential crime and. Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. This can make it impossible to track inventory using RFID, while also creating general havoc by preventing access using ID cards. Eavesdropping.
To keep your RFID credit cards safe, keep your card in an RFID shield wallet or sleeve to block RFID scanners from reading your personal information. If you don’t have one of these sleeves, try putting several RFID cards together in your wallet to make it harder for the scanner to isolate an individual card. RFID Credit Cards Are Easy Prey for Hackers, Demo Shows. News. 01 Feb 20123 mins. FirewallsMobile SecurityNetwork Security. With a simple hack and minimal equipment, a security researcher.
Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data.By understanding the basics of RFID technology, comprehending the threats posed by RFID hacking, and implementing robust protection strategies, organizations can safeguard their RFID systems and protect their valuable assets and sensitive information from .
Learn how to prevent RFID hacking with our comprehensive guide. Increase your business safety and convenience while eliminating RFID attacks. Click here! One of the biggest public fears surrounding RFID hacking is with credit and debit cards. While your RFID card is safe in your wallet, a hacker scans the card in your pocket without you knowing. The attacker can then siphon money or steal information without you knowing about it. The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and Indala.With the recent shift to contactless payment cards, more cybercriminals are turning to RFID credit card theft via scanning. This article will explain how this theft happens and provide tips on how to protect your RFID credit card from potential thefts and other common payment card frauds.
Despite demonstrations to show it's possible, documented cases of RFID credit card fraud are unknown. And as security professionals know, there is a huge gulf between potential crime and. Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. This can make it impossible to track inventory using RFID, while also creating general havoc by preventing access using ID cards. Eavesdropping.
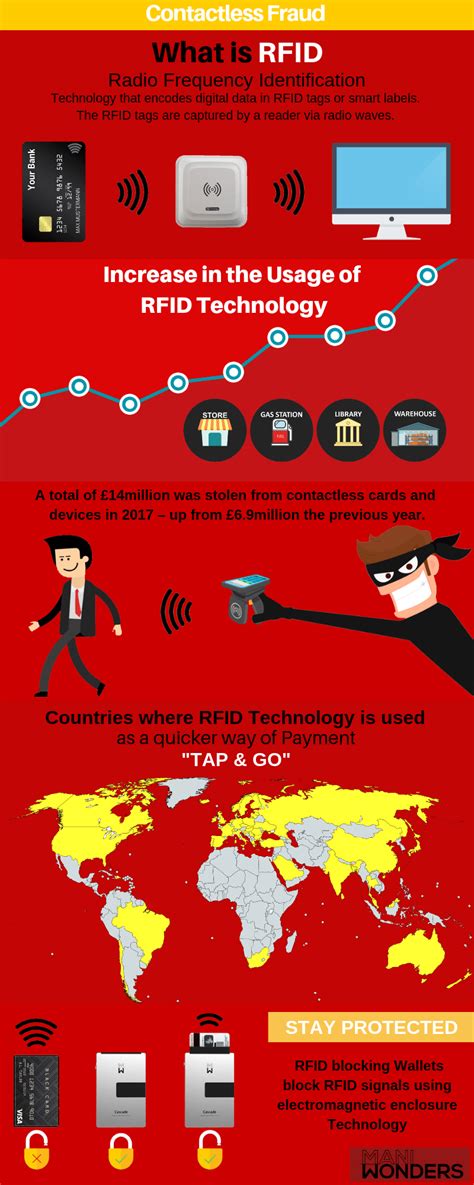
To keep your RFID credit cards safe, keep your card in an RFID shield wallet or sleeve to block RFID scanners from reading your personal information. If you don’t have one of these sleeves, try putting several RFID cards together in your wallet to make it harder for the scanner to isolate an individual card.
RFID Credit Cards Are Easy Prey for Hackers, Demo Shows. News. 01 Feb 20123 mins. FirewallsMobile SecurityNetwork Security. With a simple hack and minimal equipment, a security researcher.
Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data.

how to put data in rfid card
Dell Latitude laptops with a Broadcom 5880 security device usually have an .
rfid credit card hacking|how to block rfid scanning