can rfid chips be hacked RFID stands for Radio Frequency Identification and it's used for short-distance communication of information. It does not require line of sight to work, meaning that the RFID chip and the reader merely need to be within range of each other to communicate. There are a few main types of RFID chip: 1. . See more Philadelphia moved into the top wild-card spot thanks to losses elsewhere across the NFC. The NFC East is likely down to a two-horse race after the latest Dallas Cowboys loss .
0 · rfid scam
1 · problems with rfid technology
2 · problems with rfid
3 · is rfid safe to hack
4 · is rfid dangerous
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid scanning
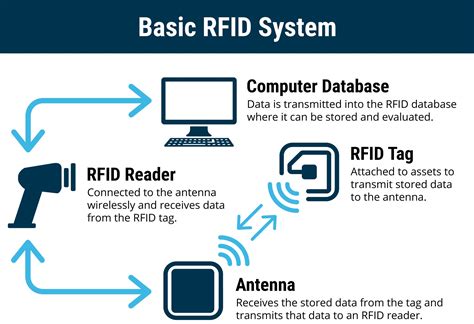
RFID stands for Radio Frequency Identification and it's used for short-distance communication of information. It does not require line of sight to work, meaning that the RFID chip and the reader merely need to be within range of each other to communicate. There are a few main types of RFID chip: 1. . See moreRFID hackers have demonstrated how easy it is to get hold of information within RFID chips. As some chips are rewritable, hackers can even delete or replace RFID information with their . See moreAs hackers have demonstrated, RFID is not impervious from attacks. There are cheap ways to build a scanner, at which point they can scan tags for sensitive information. While the panic around this form of attack may outshadow the actual chance that you'll . See moreSo, if you do want to stay on the safe side, how do you block RFID signals? In general, metal and water are the best ways to block radio . See more
By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack that will steal sensitive information or breach .Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to .
RFID hackers have demonstrated how easy it is to get hold of information within RFID chips. As some chips are rewritable, hackers can even delete or replace RFID information with their own data. It's not too tricky for a hacker build his or . By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack that will steal sensitive information or breach secured areas.
rfid scam
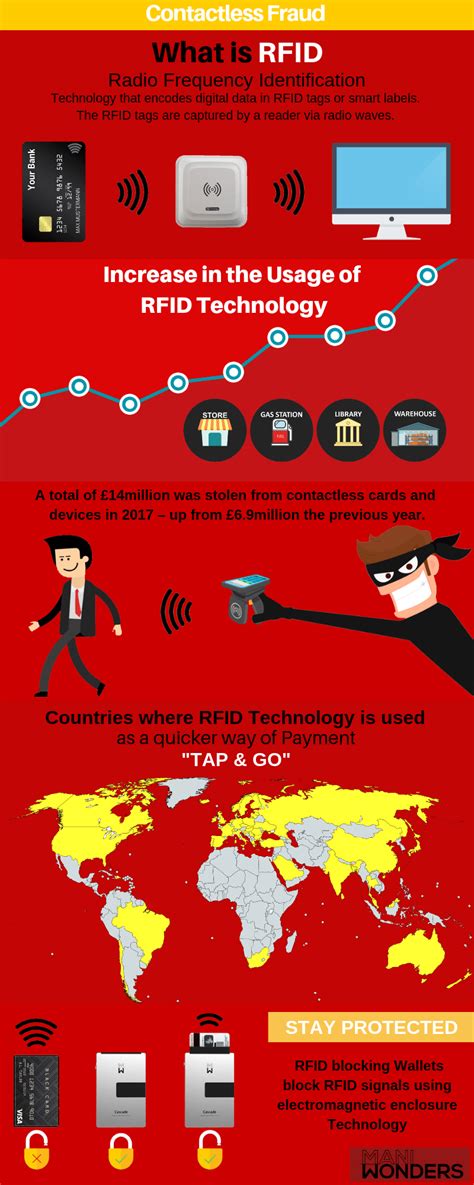
Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data. Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. This can make it impossible to track inventory using RFID, while also creating general havoc by preventing access using ID cards. Eavesdropping. A typical RFID chip can only be hacked at a range of 30 to 40 feet. Any distance farther than that and the signal is too weak, even when using an amplified reader such as those used at parking garages that automatically raise and lower gates based on RFID information.
In their popular talk at 24C3, punctuated by bursts of raucous applause, Nohl presented an overview of radio frequency identification security vulnerabilities and the process of hacking the MiFare.
For protection, RFID signals can be encrypted. The chips that will go into US passports, for example, will likely be coded to make it difficult for unauthorized readers to retrieve their. The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Contactless tags are broadly separated into low-frequency (125 kHz).By understanding the basics of RFID technology, comprehending the threats posed by RFID hacking, and implementing robust protection strategies, organizations can safeguard their RFID systems and protect their valuable assets and sensitive information from .Can RFID Chips Be Hacked? Exploring the Risks and Protections • RFID Chip Hacking • Learn about the challenges of hacking RFID chips and how to protect again.
RFID hackers have demonstrated how easy it is to get hold of information within RFID chips. As some chips are rewritable, hackers can even delete or replace RFID information with their own data. It's not too tricky for a hacker build his or . By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack that will steal sensitive information or breach secured areas.Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data.
Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. This can make it impossible to track inventory using RFID, while also creating general havoc by preventing access using ID cards. Eavesdropping. A typical RFID chip can only be hacked at a range of 30 to 40 feet. Any distance farther than that and the signal is too weak, even when using an amplified reader such as those used at parking garages that automatically raise and lower gates based on RFID information. In their popular talk at 24C3, punctuated by bursts of raucous applause, Nohl presented an overview of radio frequency identification security vulnerabilities and the process of hacking the MiFare.
For protection, RFID signals can be encrypted. The chips that will go into US passports, for example, will likely be coded to make it difficult for unauthorized readers to retrieve their.
The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Contactless tags are broadly separated into low-frequency (125 kHz).
By understanding the basics of RFID technology, comprehending the threats posed by RFID hacking, and implementing robust protection strategies, organizations can safeguard their RFID systems and protect their valuable assets and sensitive information from .
problems with rfid technology
rfid card for port entry
problems with rfid
They’re behind a Kickstarter campaign for the ChameleonMini, a device for NFC .
can rfid chips be hacked|rfid scam