hacking mifare classic cards These cards are considered fairly old and insecure by now. There’s plenty of . Relay: Relays NFC traffic between two devices using a server. One device operates as a "reader" reading an NFC tag, the other device emulates an NFC tag using the Host Card Emulation .
0 · mifare ultralight vs classic
1 · mifare classic vs desfire
2 · mifare classic download
3 · mifare classic card recovery tool
4 · mifare classic card format
5 · mifare classic 1k cards
6 · mifare classic 1k card specification
7 · mifare 1k vs 4k
How to use Quick Share: Find the file, photo, or content you want to share. Tap on the Share button. Select Quick Share. Your device will start looking for devices with Quick Share activated .

mifare ultralight vs classic
The first attack on Mifare cards is called Darkside attack, which exploit the weak pseudo-random generator on the card to discover a single . These cards are considered fairly old and insecure by now. There’s plenty of .hack Mifare Classic cards are developed, what completely jeopardized the card reputation. The first attack on Mifare cards is called Darkside attack, which exploit the weak pseudo-random generator on the card to discover a single key. This attack aims to recover one key from the.
These cards are considered fairly old and insecure by now. There’s plenty of guides online on how to crack the private keys that are supposed to make the card secure. MIFARE, is a trademark for a series of chips widely used in contactless smart cards and proximity cards. It is often incorrectly used as a synonym of RFID. MIFARE is owned by NXP semiconductors which was previously known as Philips Electronics. The reason behind this misuse is simple. CRYPTO-1 uses two 48 bits-long keys on Mifare Classic cards to encrypt the data on its sectors. Each key can be configured to be used for reading or writing on a sector.
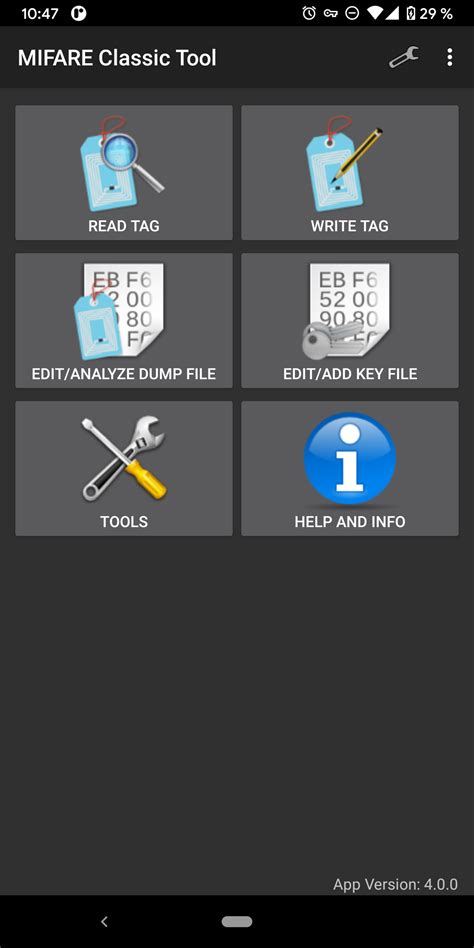
In this blog post I will cover some quick basics about NFC, Mifare Classic and how to set up everything for reading and writing a NFC tag. At the end I show you how to reprogram a vending machine's NFC tag to contain more credits.The Mifare Cracking GUI (mcgui) identifies, cracks, and clones both original and hardened Mifare Classic cards. Mcgui provides a simple user interface for existing Mifare cracking functions. The available cracking options through mcgui are the Dark Side, Hard Nested, and Nested attacks.The NFC tag I analyzed is a so called “Mifare Classic 1k” tag. 1k stands for the size of data the tag can store. There are also other types like the “Mifare Classic 4k” and the “Mifare Mini” each having a different memory size. Episode 4 of Proxmark 3 Basics: Learn how to identify, crack, read and clone MIFARE Classic® cards. The Proxmark 3 RDV4.01 main firmware branches integrate all known MIFARE Classic® cracking techniques, and this episode deep dives into each one.
In this Tradecraft tutorial, we will be decyphering and emulating Mifare Classic 1K cards using the Proxmark3 RDV4 and the RFID Tools Android App by RRG. Thi.hack Mifare Classic cards are developed, what completely jeopardized the card reputation. The first attack on Mifare cards is called Darkside attack, which exploit the weak pseudo-random generator on the card to discover a single key. This attack aims to recover one key from the.
These cards are considered fairly old and insecure by now. There’s plenty of guides online on how to crack the private keys that are supposed to make the card secure. MIFARE, is a trademark for a series of chips widely used in contactless smart cards and proximity cards. It is often incorrectly used as a synonym of RFID. MIFARE is owned by NXP semiconductors which was previously known as Philips Electronics. The reason behind this misuse is simple.
CRYPTO-1 uses two 48 bits-long keys on Mifare Classic cards to encrypt the data on its sectors. Each key can be configured to be used for reading or writing on a sector.
In this blog post I will cover some quick basics about NFC, Mifare Classic and how to set up everything for reading and writing a NFC tag. At the end I show you how to reprogram a vending machine's NFC tag to contain more credits.

The Mifare Cracking GUI (mcgui) identifies, cracks, and clones both original and hardened Mifare Classic cards. Mcgui provides a simple user interface for existing Mifare cracking functions. The available cracking options through mcgui are the Dark Side, Hard Nested, and Nested attacks.
The NFC tag I analyzed is a so called “Mifare Classic 1k” tag. 1k stands for the size of data the tag can store. There are also other types like the “Mifare Classic 4k” and the “Mifare Mini” each having a different memory size. Episode 4 of Proxmark 3 Basics: Learn how to identify, crack, read and clone MIFARE Classic® cards. The Proxmark 3 RDV4.01 main firmware branches integrate all known MIFARE Classic® cracking techniques, and this episode deep dives into each one.
mifare classic vs desfire
how to login with smart card windows 10
25 pcs/set Zelda Breath of The Wild Amiibo NFC Game Cards For Nintendo Switch. Brand .
hacking mifare classic cards|mifare 1k vs 4k