which type of authentication includes smart cards Study with Quizlet and memorize flashcards containing terms like What is an . See the latest NFL Standings by Division, Conference and League. Find current or past season NFL standings by team.Levi's Stadium
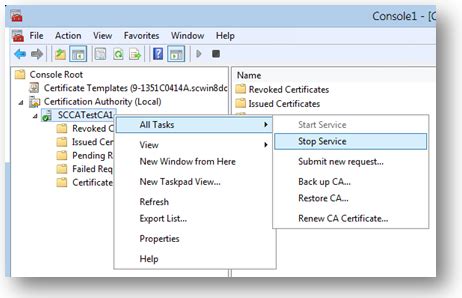
0 · windows 10 smart card setup
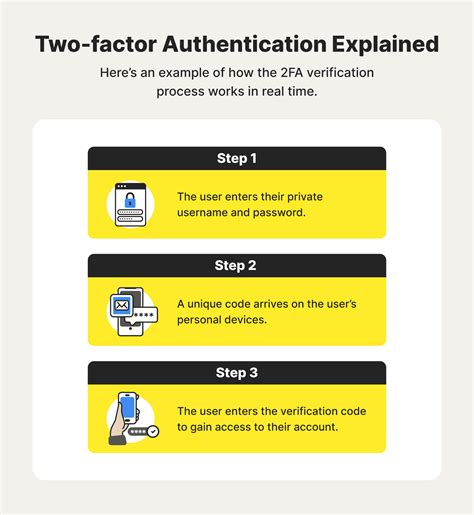
1 · what is smart card authentication
2 · what is an example of two factor authentication 2fa
3 · what is an example of a logical access control
4 · true or false a smart card is an example of a logical access control
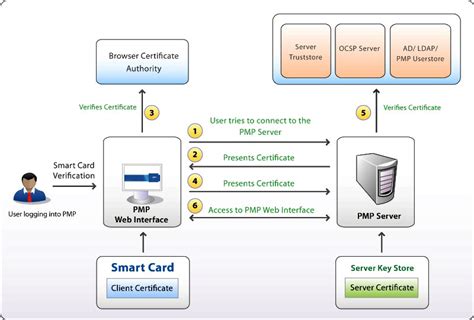
5 · smart card based authentication
6 · smart card authentication step by
7 · authenticate using your smart card
Greener NFC card printing. You can now have custom printed NFC cards free of metal and plastic creating a recyclable solution to reduce your company’s environmental impact. Introducing Pulper, made of wood fibre from .
Authentication by OWNERSHIP is based on something you have, such as a smart card, a key, a badge, or either a synchronous or asynchronous token.Authentication by characteristics/biometrics is based on something you have, such .
Study with Quizlet and memorize flashcards containing terms like What is an .Authentication by characteristics/biometrics is based on something you have, such as a smart card, a key, a badge, or either a synchronous or asynchronous token.
Study with Quizlet and memorize flashcards containing terms like What is an example of a logical access control?, The ___________ is the central part of a computing environment's hardware, .Authentication by OWNERSHIP is based on something you have, such as a smart card, a key, a badge, or either a synchronous or asynchronous token.
Authentication by characteristics/biometrics is based on something you have, such as a smart card, a key, a badge, or either a synchronous or asynchronous token.Study with Quizlet and memorize flashcards containing terms like What is an example of a logical access control?, The ___________ is the central part of a computing environment's hardware, software, and firmware that enforces access control., Which type of authentication includes smart cards? and more.
Smart cards may provide strong security authentication for single sign-on (SSO) within organizations. Numerous nations have deployed smart cards throughout their populations. The universal integrated circuit card (UICC) for mobile phones, installed as pluggable SIM card or embedded eSIM, is also a type of smart card.
Certificate-based authentication is an encrypted method that enables devices and people to identify themselves to other devices and systems. Two common examples are a smart card or when an employee’s device sends a digital certificate to a network or server. Using a smart card in conjunction with a password can add an extra layer of security to protect sensitive patient or customer data. An additional layer of security can be provided here by AI, both through scanning for compromised devices as well as performing risk-based authentication.Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and software on the workstation.A smart card is a secure microcontroller that is typically used for generating, storing and operating on cryptographic keys. Smart card authentication provides users with smart card devices for the purpose of authentication. Users connect their smart card to a host computer.
Token-based authentication enables users to log in to accounts using a physical device, such as a smartphone, security key or smart card. It can be used as part of MFA or to provide a passwordless experience.
smart cards for hospitals
windows 10 smart card setup
Pick the right kind of smart card: Choose a smart card type based on how much it can store, its security, and if it works with your things. Also pick card readers: Choose readers that work with the card type and security you need.Authentication by OWNERSHIP is based on something you have, such as a smart card, a key, a badge, or either a synchronous or asynchronous token.
Authentication by characteristics/biometrics is based on something you have, such as a smart card, a key, a badge, or either a synchronous or asynchronous token.Study with Quizlet and memorize flashcards containing terms like What is an example of a logical access control?, The ___________ is the central part of a computing environment's hardware, software, and firmware that enforces access control., Which type of authentication includes smart cards? and more.Smart cards may provide strong security authentication for single sign-on (SSO) within organizations. Numerous nations have deployed smart cards throughout their populations. The universal integrated circuit card (UICC) for mobile phones, installed as pluggable SIM card or embedded eSIM, is also a type of smart card.
Certificate-based authentication is an encrypted method that enables devices and people to identify themselves to other devices and systems. Two common examples are a smart card or when an employee’s device sends a digital certificate to a network or server.
Using a smart card in conjunction with a password can add an extra layer of security to protect sensitive patient or customer data. An additional layer of security can be provided here by AI, both through scanning for compromised devices as well as performing risk-based authentication.Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and software on the workstation.A smart card is a secure microcontroller that is typically used for generating, storing and operating on cryptographic keys. Smart card authentication provides users with smart card devices for the purpose of authentication. Users connect their smart card to a host computer.
Token-based authentication enables users to log in to accounts using a physical device, such as a smartphone, security key or smart card. It can be used as part of MFA or to provide a passwordless experience.
what is smart card authentication
smart chip card reader price
You should totally look into writing NFC tags with your phone! Most androids and all iPhones are capable of writing NFC tags, and if the batch you bought didn't work, there's a chance you can rewrite them with the villager they're supposed .
which type of authentication includes smart cards|what is an example of a logical access control