mifare classic card recovery mifare classic card recovery tools beta v0 1 zip is a Windows tool for offline cracking of MIFARE Classic RFID tags. It is based on the research of Nethemba and the implementation of MFOC. Another step-by-step guide on how the more advanced 13.56MHz cards can be copied (and, of course, which equipment you need) You’ll learn to clone cards (NFC or RFID cloner) at your office desk! The Impact of RFID .
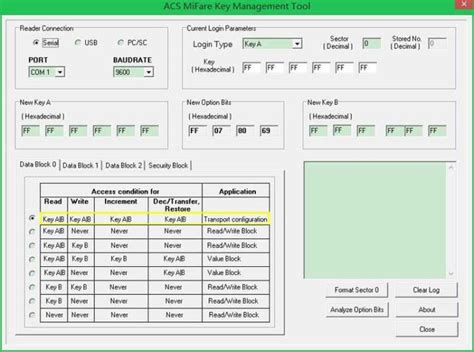
0 · acs MIFARE key management tool
1 · MIFARE windows tool download
2 · MIFARE classic tool windows
3 · MIFARE classic tool keys
4 · MIFARE classic tool key file
5 · MIFARE classic tool emulate
6 · MIFARE classic tool download
7 · MIFARE classic tool clone card
$2.99
mifare classic card recovery tools beta v0 1 zip is a Windows tool for offline cracking of MIFARE Classic RFID tags. It is based on the research of Nethemba and the implementation of MFOC.It uses two methods to recover keys: * Darkside attack using parity bits leakage. * Nested Authentication using encrypted nonce leakage. The tool is intented as an alternative frontend .Due to some weaknesses in MIFARE Classic, you can retrieve all the keys (A and B) of a tag with tools like the Proxmark3 or normal RFID-Readers and some special software (mfcuk, mfoc). The application comes with standard key files called std.keys and extended-std.keys , which contain the well known keys and some standard keys from a short .mifare classic card recovery tools beta v0 1 zip is a Windows tool for offline cracking of MIFARE Classic RFID tags. It is based on the research of Nethemba and the implementation of MFOC.
It uses two methods to recover keys: * Darkside attack using parity bits leakage. * Nested Authentication using encrypted nonce leakage. The tool is intented as an alternative frontend to Mifare classic key recovery, providing an automated solution with minimal user interaction.
This program allow to recover authentication keys from MIFARE Classic card. Please note MFOC is able to recover keys from target only if it have a known key: default one (hardcoded in MFOC) or custom one (user provided using command line).
MFKey32 is the name of a tool/algorithm used to recover the MIFARE Classic keys from the reader’s Crypto-1 nonce pairs. It works by recovering the initial state of the Crypto-1 Linear Feedback Shift Register, which contains the key.
Chose your Mifare classic saved file. At thismpoint app only supports Mifare classic 1k with 4 byte UID. This will write UID and vendor info, with correct checksum.MIFARE Classic key recovery tool. Flipper Zero MFKey. This application allows you to calculate the keys of MIFARE Classic cards using the Mfkey32 and Nested algorithms directly on your Flipper Zero. After collecting the nonces using the Extract MF Keys feature of the NFC app, they can be used to calculate the keys to the card in the MFKey app.
I successfully cloned my Mifare card on gen1a fob which i bought from online but reader doesn't accept my cloned fob. here's what i did: I used "hf mf autopwn" command and it successfully recovered all the key in A and B. but the recovered keys were all the same one key. The first attack on Mifare cards is called Darkside attack, which exploit the weak pseudo-random generator on the card to discover a single key. This attack aims to recover one key from the.
MiFare Classic Universal toolKit (MFCUK). Contribute to nfc-tools/mfcuk development by creating an account on GitHub.
Due to some weaknesses in MIFARE Classic, you can retrieve all the keys (A and B) of a tag with tools like the Proxmark3 or normal RFID-Readers and some special software (mfcuk, mfoc). The application comes with standard key files called std.keys and extended-std.keys , which contain the well known keys and some standard keys from a short .mifare classic card recovery tools beta v0 1 zip is a Windows tool for offline cracking of MIFARE Classic RFID tags. It is based on the research of Nethemba and the implementation of MFOC.It uses two methods to recover keys: * Darkside attack using parity bits leakage. * Nested Authentication using encrypted nonce leakage. The tool is intented as an alternative frontend to Mifare classic key recovery, providing an automated solution with minimal user interaction.
This program allow to recover authentication keys from MIFARE Classic card. Please note MFOC is able to recover keys from target only if it have a known key: default one (hardcoded in MFOC) or custom one (user provided using command line).MFKey32 is the name of a tool/algorithm used to recover the MIFARE Classic keys from the reader’s Crypto-1 nonce pairs. It works by recovering the initial state of the Crypto-1 Linear Feedback Shift Register, which contains the key. Chose your Mifare classic saved file. At thismpoint app only supports Mifare classic 1k with 4 byte UID. This will write UID and vendor info, with correct checksum.
MIFARE Classic key recovery tool. Flipper Zero MFKey. This application allows you to calculate the keys of MIFARE Classic cards using the Mfkey32 and Nested algorithms directly on your Flipper Zero. After collecting the nonces using the Extract MF Keys feature of the NFC app, they can be used to calculate the keys to the card in the MFKey app. I successfully cloned my Mifare card on gen1a fob which i bought from online but reader doesn't accept my cloned fob. here's what i did: I used "hf mf autopwn" command and it successfully recovered all the key in A and B. but the recovered keys were all the same one key. The first attack on Mifare cards is called Darkside attack, which exploit the weak pseudo-random generator on the card to discover a single key. This attack aims to recover one key from the.
does nfc reader make amiibos
Download Credit Card Reader NFC (EMV) 5.5.1 APK. App: Credit Card Reader Version: 5.5.1 (130) . This app is a useful tool for those who want to access and view the public data stored on their NFC-compliant EMV banking cards .
mifare classic card recovery|MIFARE classic tool clone card