skimming a card with nfc payment NFC/RFID skimming is where hackers/skimmers/bad guys intercept the radio wave communication between devices or simply read the radio waves that a NFC or RFID enabled device puts out. The bad guy's reader reads the data put out from your device or debit/credit card.
Entering the NFL Week 11 schedule, it's still a four-team race in the division, making it the most competitive division in the NFL this season from top to bottom. The 6-4 Arizona .The National Football League playoffs for the 2017 season began with the wild-card round on January 6, 2018, and concluded with Super Bowl LII on February 4, 2018, when the Philadelphia Eagles defeated the New England Patriots at U.S. Bank Stadium in Minneapolis, Minnesota. Several teams broke long . See more
0 · what is nfc skimming
1 · nfc skimming risks
2 · nfc phone payments security
3 · nfc fraudulent payments
4 · how secure are nfc payments
5 · credit card skimming scam
6 · credit card skimming devices
7 · are nfc payment methods safe
$19.99

However, as opposed to regular card skimming, NFC communication is encrypted and tokenized – meaning that a card can hardly be duplicated thanks to its information being hidden.Embracing modern payment technologies can significantly reduce the risk of credit card skimming. Contactless payments offer a more secure alternative by minimizing physical .Embracing modern payment technologies can significantly reduce the risk of credit card skimming. Contactless payments offer a more secure alternative by minimizing physical contact between your card and the payment terminal. . Near Field Communication (NFC): Contactless payments use NFC technology, which enables you to tap your card or device . However, as opposed to regular card skimming, NFC communication is encrypted and tokenized – meaning that a card can hardly be duplicated thanks to its information being hidden.
In a skimming attack, someone with an NFC device gets physically close enough to your phone or contactless card to trigger a transaction. For example, a thief could walk past you in the street and initiate a payment from your mobile wallet via a handheld card reader.NFC/RFID skimming is where hackers/skimmers/bad guys intercept the radio wave communication between devices or simply read the radio waves that a NFC or RFID enabled device puts out. The bad guy's reader reads the data put out from your device or debit/credit card. Skimming involves capturing an individual’s sensitive information from payment cards or identification credentials like an NFC reader. Most times, skimming attacks occur through a rogue NFC reader. This is a corrupt device designed to emulate a legitimate NFC reader. Contactless payments, whether through a tap-and-go card or a mobile wallet like Apple Pay or Google Pay, use near-field communication (NFC) technology to securely transmit your payment information without the need to insert or swipe your card.
Tap-to-pay, or contactless payment, uses near-field communication (NFC) to transmit encrypted payment data wirelessly from a chip in the card or smartphone to a secure payment terminal. This technology makes it extremely difficult for scammers to intercept and decode transaction data.Skimming occurs when devices illegally installed on or inside ATMs, point-of-sale (POS) terminals, or fuel pumps capture card data and record cardholders’ PIN entries. Criminals use the data to.
what is nfc skimming
Some security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or personal information simply by walking within a few feet of you. To help avoid coming into contact with a card skimmer, try to use payment terminals that are supervised by security cameras or skip using the card reader altogether and make a Near Field Communication(NFC) payment.Embracing modern payment technologies can significantly reduce the risk of credit card skimming. Contactless payments offer a more secure alternative by minimizing physical contact between your card and the payment terminal. . Near Field Communication (NFC): Contactless payments use NFC technology, which enables you to tap your card or device . However, as opposed to regular card skimming, NFC communication is encrypted and tokenized – meaning that a card can hardly be duplicated thanks to its information being hidden.
In a skimming attack, someone with an NFC device gets physically close enough to your phone or contactless card to trigger a transaction. For example, a thief could walk past you in the street and initiate a payment from your mobile wallet via a handheld card reader.NFC/RFID skimming is where hackers/skimmers/bad guys intercept the radio wave communication between devices or simply read the radio waves that a NFC or RFID enabled device puts out. The bad guy's reader reads the data put out from your device or debit/credit card.
Skimming involves capturing an individual’s sensitive information from payment cards or identification credentials like an NFC reader. Most times, skimming attacks occur through a rogue NFC reader. This is a corrupt device designed to emulate a legitimate NFC reader. Contactless payments, whether through a tap-and-go card or a mobile wallet like Apple Pay or Google Pay, use near-field communication (NFC) technology to securely transmit your payment information without the need to insert or swipe your card. Tap-to-pay, or contactless payment, uses near-field communication (NFC) to transmit encrypted payment data wirelessly from a chip in the card or smartphone to a secure payment terminal. This technology makes it extremely difficult for scammers to intercept and decode transaction data.
Skimming occurs when devices illegally installed on or inside ATMs, point-of-sale (POS) terminals, or fuel pumps capture card data and record cardholders’ PIN entries. Criminals use the data to. Some security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or personal information simply by walking within a few feet of you.
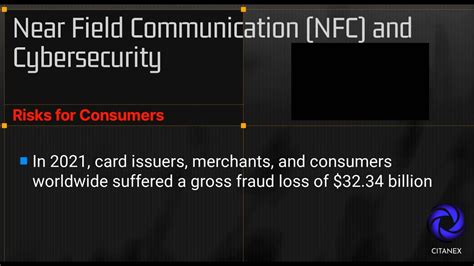
nfc skimming risks
nfc phone payments security
nfc fraudulent payments
Guide for NFC cards - Flipper zero magic NFC. This guide is for the ones who wish to buy their own magic NFC cards. It should include all the basic information on what cards to look out for. .
skimming a card with nfc payment|nfc fraudulent payments