smart card based authentication For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers. This topic includes information about: Credential provider architecture. Smart card subsystem architecture. Credential provider architecture. You can listen to live Auburn Tigers games online or on the radio dial. With 54 stations in the network, the Auburn Sports Network represents one of the biggest and most-listened to college sports network in the South. All home and away .
0 · what is smart card authentication
1 · smart card two factor authentication
2 · smart card certificate authentication
3 · smart card based identification system
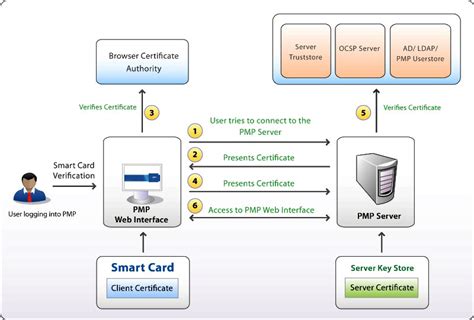
4 · smart card authentication step by
5 · smart card authentication process
6 · configure smart card authentication
7 · authenticate using your smart card
Statewide coverage is the hallmark of the Auburn Sports Network's exclusive .
For smart cards, Windows supports a provider architecture that meets the .
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers. This topic includes information about: Credential provider architecture. Smart card subsystem architecture. Credential provider architecture.Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and software on the workstation. Smart cards are tamper-resistant portable storage devices that can enhance the security of tasks such as authenticating clients, signing code, securing e-mail, and signing in with a Windows domain account. Smart cards provide: Tamper-resistant storage for protecting private keys and other forms of personal information.
Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and industry certifications.
Access Control via Smart Card Authentication. Thales's range of certificate-based smart cards offer strong multi-factor authentication in a traditional credit card form factor and enable organizations to address their PKI security needs. Table of Content. Understanding Smart Card Authentication: How Does Smart Card Authentication Work? The process: Implementing Smart Card Authentication: Testing and using the system: Best Practices for Smart Card Authentication: Conclusion: Nowadays, cybersecurity is .
nfc tag on sticker for lg tv
what is smart card authentication
As a National eID card, smart health card, residence permit, or electronic passport, smart card technology offers more robust identification and authentication tools for both authorities' and citizens' benefits. This technology, such as a driver's license or a tachograph card, contributes to road safety. Over 10B smart cards shipped in 2022.Authentication based on smart cards is an alternative to passwords. You can store user credentials on a smart card in the form of a private key and a certificate, and special software and hardware is used to access them.Smart cards, such as debit cards, are often used with a personal identification number (PIN). Organizations also use them for security purposes, as MFA tokens and for authenticating single sign-on users and enabling passwordless authentication. Types of smart cardsHow Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.
For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers. This topic includes information about: Credential provider architecture. Smart card subsystem architecture. Credential provider architecture.Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and software on the workstation.
Smart cards are tamper-resistant portable storage devices that can enhance the security of tasks such as authenticating clients, signing code, securing e-mail, and signing in with a Windows domain account. Smart cards provide: Tamper-resistant storage for protecting private keys and other forms of personal information. Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and industry certifications.
Access Control via Smart Card Authentication. Thales's range of certificate-based smart cards offer strong multi-factor authentication in a traditional credit card form factor and enable organizations to address their PKI security needs. Table of Content. Understanding Smart Card Authentication: How Does Smart Card Authentication Work? The process: Implementing Smart Card Authentication: Testing and using the system: Best Practices for Smart Card Authentication: Conclusion: Nowadays, cybersecurity is .
As a National eID card, smart health card, residence permit, or electronic passport, smart card technology offers more robust identification and authentication tools for both authorities' and citizens' benefits. This technology, such as a driver's license or a tachograph card, contributes to road safety. Over 10B smart cards shipped in 2022.Authentication based on smart cards is an alternative to passwords. You can store user credentials on a smart card in the form of a private key and a certificate, and special software and hardware is used to access them.
nfc tag on washing machine
smart card two factor authentication
nfc tag radio equipment directive
smart card certificate authentication
How to listen to Alabama vs. Mercer game on radio? Alabama fans can catch the action live on Tide 100.9 FM and WTBC 1230 AM, known as "The Home of Alabama Sports." .
smart card based authentication|smart card two factor authentication