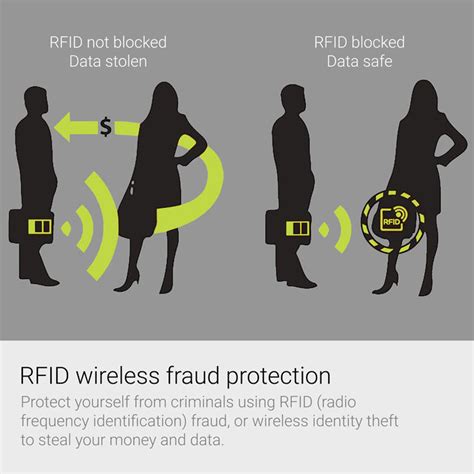
rfid scanner thieves While RFID skimming should be the least of your worries, it’s important to take steps to protect against the very real threats of credit card fraud and other forms of identity theft. Be proactive with automatic, 24/7 monitoring of your credit report and credit score, so you’ll . See more Weekly coverage of Auburn football from Auburn Sports Network begins Thursday nights at 6 p.m. CT for Tiger Talk. Andy Burcham and Brad Law will be joined weekly by head coach Hugh Freeze and other in-season .
0 · what does rfid theft do
1 · rfid theft hack
2 · rfid theft
3 · rfid scam
4 · rfid chip scanning
5 · how to prevent rfid theft
6 · how do rfid thefts happen
7 · credit card rfid theft
Talkin' Tide. Talkin' Tide covers Alabama football twice a week with Tuscaloosa News columnist Chase Goodbread and BamaOnLine.com senior analyst Travis Reier. The 'Bama Beat. .Statewide coverage is the hallmark of the Auburn Sports Network's exclusive coverage of Auburn football. All home and away games are broadcast across the entire state of Alabama plus portions of .
what does rfid theft do
Radio-Frequency Identification (RFID) involves the use of radio waves to read and capture information stored on an electronic chip attached to an object. RFID chips, or “tags,” can be read via scanning devices from up to several feet away. These chips have been used by businesses for years to manage inventory . See more
Some security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or personal information simply by walking within a few feet of you. It’s a scary thought, . See moreWhile RFID skimming should be the least of your worries, it’s important to take steps to protect against the very real threats of credit card fraud and other forms of identity theft. Be proactive with automatic, 24/7 monitoring of your credit report and credit score, so you’ll . See more What Is RFID Theft? RFID stands for Radio Frequency Identification. RFID theft occurs when someone uses their own RFID reader to trigger the chip in your credit card; a .
rfid chip number
rfid theft hack
Summary: Products such as “RFID wallets” claim to prevent frauds and scams like RFID skimming, in which thieves steal information off your chip-embedded credit card. Be wary of these claims; there are better forms of identity theft .
What Is RFID Theft? RFID stands for Radio Frequency Identification. RFID theft occurs when someone uses their own RFID reader to trigger the chip in your credit card; a process called ‘skimming’ or ‘digital pickpocketing.’ The card thinks it is being asked for information to carry out a sale. Grimes says tracking RFID crime is just about impossible — it's hard to know how someone's information was stolen. But he says the reason it's unlikely to happen is simple: thieves don't want. Scam: Card-skimming thieves can make fraudulent purchases with information read from RFID-enabled credit cards carried in pockets and purses.Wireless identity theft, also known as contactless identity theft or RFID identity theft, is a form of identity theft described as "the act of compromising an individual’s personal identifying information using wireless (radio frequency) mechanics."
Scanning is a type of credit card fraud in which cybercriminals use illegal card readers to activate RFID chips on unsuspecting victims’ credit cards and extract payment details. For this to happen, the hackers must be within the card’s read range, which is typically 5–6 inches.
Store multiple RFID cards close to each other in your wallet to make them harder to read, or carry them in your front pocket to discourage thieves. Use an RFID shield wallet or protective sleeve, wrap it in foil, or store your card next . RFID theft, also known as skimming or electronic pickpocketing, takes advantage of the vulnerabilities in RFID technology to steal personal information from RFID-enabled cards or tags. Understanding how RFID theft works is crucial .Using an RFID scanner, a thief can “skim” your card or passport information from a few feet away, often without your knowledge. This stolen information can be used to make purchases, create counterfeit IDs, or steal your identity.
Radio frequency identification (RFID) technology is present in a ton of products, from the passive security tags stuck to the laundry detergent you bought at Target to the card reader that. Summary: Products such as “RFID wallets” claim to prevent frauds and scams like RFID skimming, in which thieves steal information off your chip-embedded credit card. Be wary of these claims; there are better forms of identity theft . What Is RFID Theft? RFID stands for Radio Frequency Identification. RFID theft occurs when someone uses their own RFID reader to trigger the chip in your credit card; a process called ‘skimming’ or ‘digital pickpocketing.’ The card thinks it is being asked for information to carry out a sale.
amazon rfid chips
Grimes says tracking RFID crime is just about impossible — it's hard to know how someone's information was stolen. But he says the reason it's unlikely to happen is simple: thieves don't want.
Scam: Card-skimming thieves can make fraudulent purchases with information read from RFID-enabled credit cards carried in pockets and purses.
Wireless identity theft, also known as contactless identity theft or RFID identity theft, is a form of identity theft described as "the act of compromising an individual’s personal identifying information using wireless (radio frequency) mechanics."
Scanning is a type of credit card fraud in which cybercriminals use illegal card readers to activate RFID chips on unsuspecting victims’ credit cards and extract payment details. For this to happen, the hackers must be within the card’s read range, which is typically 5–6 inches. Store multiple RFID cards close to each other in your wallet to make them harder to read, or carry them in your front pocket to discourage thieves. Use an RFID shield wallet or protective sleeve, wrap it in foil, or store your card next . RFID theft, also known as skimming or electronic pickpocketing, takes advantage of the vulnerabilities in RFID technology to steal personal information from RFID-enabled cards or tags. Understanding how RFID theft works is crucial .Using an RFID scanner, a thief can “skim” your card or passport information from a few feet away, often without your knowledge. This stolen information can be used to make purchases, create counterfeit IDs, or steal your identity.
rfid theft

RFID Tags. RFID (Radio Frequency Identification) is a robust technology that is increasingly .
rfid scanner thieves|credit card rfid theft