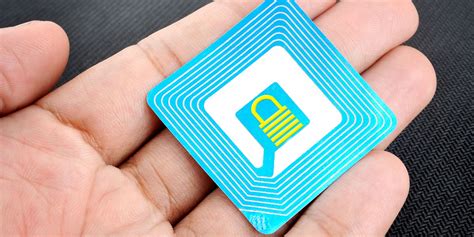
tags locking to block unauthorised writing rfid Eavesdropping is a technique used by attackers to intercept and decode the radio signals exchanged between RFID tags and readers. By capturing these signals, hackers can gain unauthorized access to sensitive information, such as personal identification numbers or confidential data.
Proceed as follows: First open the Settings app on your iPhone. Then select the option “Control Center”. Scroll down and tap the green plus button to the left of “NFC Tag Reader”. The iPhone XS (Max), iPhone XR, iPhone 11 as well as .
0 · rfid hacking protection
1 · rfid hacking examples
2 · rfid hacking definition
3 · rfid hacking
4 · rfid attacks
5 · how to protect sensitive rfid
6 · how to protect rfid data
7 · how to prevent rfid
The following table contains the 45 known Nintendo 3DS handheld video games that contain support for added amiibo unlockable content and functionality. Original 3DS Family hardware can use the Nintendo 3DS NFC Reader/Writer .
rfid hacking protection
RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards.Generic Attacks. Sniffing of the communication between transponder and reader. .
RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards.
now tv smart box sd card
Generic Attacks. Sniffing of the communication between transponder and reader. Counterfeiting of the communication. Obtain UID, user data and meta data. Basic attack on structures and tags. Replay attack to fool the access control systems. The reader must supply a specific key before the tag will reveal any personal information, blocking potential skimming. This method is commonly applied to protect the sensitive data stored in passports from being read by outsiders.Eavesdropping is a technique used by attackers to intercept and decode the radio signals exchanged between RFID tags and readers. By capturing these signals, hackers can gain unauthorized access to sensitive information, such as personal identification numbers or confidential data. Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. This can make it impossible to track inventory using RFID, while also creating general havoc by preventing access using ID cards. Eavesdropping.
When properly utilized, foil can act as a barrier to block or significantly weaken RFID signals, preventing them from reaching an RFID tag and reading its data. The foil creates a Faraday cage effect, which is a conductive enclosure that effectively blocks electromagnetic fields from penetrating it. RFID blocking refers to the use of specialized products or materials that aim to prevent the unauthorized reading of RFID-enabled cards, passports, and other items. In this article, we will explore the concept of RFID blocking, how it works, and its benefits and limitations.
RFID blocking is essential in preventing unauthorized access to sensitive information, such as in credit cards and passports. Wallets and passport covers that incorporate RFID-blocking materials are designed to stop skimming attacks, where criminals attempt to steal information through unintentional RFID scans. A third practice is to lock your RFID tags to prevent unauthorized changes or erasure of the data. Locking is a feature that allows you to set different levels of access and protection.
An RFID virus can either destroy or disclose the tags data stored in the database disrupt the service or block the communication between the database and the reader. To protect your RIFD database, make sure you mitigate database related vulnerabilities and risks. RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards.Generic Attacks. Sniffing of the communication between transponder and reader. Counterfeiting of the communication. Obtain UID, user data and meta data. Basic attack on structures and tags. Replay attack to fool the access control systems. The reader must supply a specific key before the tag will reveal any personal information, blocking potential skimming. This method is commonly applied to protect the sensitive data stored in passports from being read by outsiders.
Eavesdropping is a technique used by attackers to intercept and decode the radio signals exchanged between RFID tags and readers. By capturing these signals, hackers can gain unauthorized access to sensitive information, such as personal identification numbers or confidential data. Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. This can make it impossible to track inventory using RFID, while also creating general havoc by preventing access using ID cards. Eavesdropping.
When properly utilized, foil can act as a barrier to block or significantly weaken RFID signals, preventing them from reaching an RFID tag and reading its data. The foil creates a Faraday cage effect, which is a conductive enclosure that effectively blocks electromagnetic fields from penetrating it.
RFID blocking refers to the use of specialized products or materials that aim to prevent the unauthorized reading of RFID-enabled cards, passports, and other items. In this article, we will explore the concept of RFID blocking, how it works, and its benefits and limitations.
RFID blocking is essential in preventing unauthorized access to sensitive information, such as in credit cards and passports. Wallets and passport covers that incorporate RFID-blocking materials are designed to stop skimming attacks, where criminals attempt to steal information through unintentional RFID scans. A third practice is to lock your RFID tags to prevent unauthorized changes or erasure of the data. Locking is a feature that allows you to set different levels of access and protection.

newest update won't recognize smart card
S.A.S. WAKDEV CEO: Julien Veuillet Answering machine: +33.652283944 E .
tags locking to block unauthorised writing rfid|rfid hacking