issues with rfid tags It might seem like full steam ahead for RFID adoption in many industries, but there are some potential speed bumps in terms of growth. Here are four key challenges . See more The 8 Best Credit Card Readers For Android Phones & Tablets. More companies are starting to understand the importance of offering Android .When considering an iPhone credit card reader, there are a few essential hardware features to look out for: 1. EMV chip reader:An EMV chip reader is a must-have for any business that wants to accept credit and debit cards. EMV is short for Europay, Mastercard and Visa and is the global standard for credit and . See more
0 · rfid tag working principle
1 · rfid problems and solutions
2 · rfid privacy and security issues
3 · rfid myths and facts debunked
4 · rfid issues and concerns
5 · rfid is vulnerable to
6 · rfid disadvantages
7 · rfid advantages and disadvantages
Near Field Communication (NFC) technology operates on the principles of magnetic field induction and radio frequency . See more
According to a recent RFID market report, the global market for RFID tags, readers and softwareis expected to reach .7 billion this year and expand to .4 billion by 2026. Here are some of the trends driving that growth. See moreIt might seem like full steam ahead for RFID adoption in many industries, but there are some potential speed bumps in terms of growth. Here are four key challenges . See more
If you want to find out the latest trends in the RFID industry—as well as solutions to existing challenges—you need to attend RFID Journal LIVE! 2021. This . See moreThis post aims to highlight several important RFID related security issues. RFID Counterfeiting: depending on the computing power, RFID can be classified into three categories: Basic tags; . There are some important trends—and some issues—facing the industry. Key Takeaways. The RFID industry is growing fast and will continue to grow over the next five years. UHF tags are the fastest-growing segment, while logistics and supply chain management is the fastest-growing application.
This post aims to highlight several important RFID related security issues. RFID Counterfeiting: depending on the computing power, RFID can be classified into three categories: Basic tags; Tags that uses symmetric keys; Tags that uses public-key; Since basic tags do not use any encryption, they can be counterfeited easily. RFID chips can be a great asset, but they also come with a number of potential risks and dangers. Environmental factors are the most common cause of RFID interference problems. While there are some benefits of using RFID tags for inventory management, the technology also comes with several disadvantages that hinder usability and accuracy.Many factors can affect RFID systems, and the most common problems include signal interference, improper tag placement, insufficient power supply, and environmental factors. Understanding the root causes of these problems is critical to preventing downtime and ensuring optimal performance. 1. Signal Interference in RFID Systems.The ability of RFID tags to store and transmit sensitive information raises privacy concerns. Regulatory frameworks like GDPR in Europe have strict requirements about how data can be collected, stored, and shared.
A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and reader don't have to touch. Some RFID tags can be powered by a . The RFID tags allow healthcare facilities to track the locations of at-risk patients for safety or identify a patient without disturbing them, and the barcodes are used by nurses to quickly scan and verify a patient's identity and medical record number. Myth #4: With RFID, You’ll Always Have Real-Time Information on Item Locations.
Among all, cost and security of RFID technology are of major concern. Manufacturing industries must explore new solutions to limit the cost and to boost the security of RFID tags. In this way, supply chain stores and retailing companies would experience seamless integration in . RFID tags and the General Data Protection Regulation - personal data or not? RFID tags can be considered, under the General Data Protection Regulation 2018 (GDPR), an online identifier similar to cookies.If you already have an RFID system installed and you are experiencing problems, a specialist will troubleshoot your system and identify the possible causes of interference. The two types of problems RFID relies on wireless transmission of signals between readers and tags so interference can prevent the system from working effectively.
There are some important trends—and some issues—facing the industry. Key Takeaways. The RFID industry is growing fast and will continue to grow over the next five years. UHF tags are the fastest-growing segment, while logistics and supply chain management is the fastest-growing application.This post aims to highlight several important RFID related security issues. RFID Counterfeiting: depending on the computing power, RFID can be classified into three categories: Basic tags; Tags that uses symmetric keys; Tags that uses public-key; Since basic tags do not use any encryption, they can be counterfeited easily.

RFID chips can be a great asset, but they also come with a number of potential risks and dangers. Environmental factors are the most common cause of RFID interference problems. While there are some benefits of using RFID tags for inventory management, the technology also comes with several disadvantages that hinder usability and accuracy.Many factors can affect RFID systems, and the most common problems include signal interference, improper tag placement, insufficient power supply, and environmental factors. Understanding the root causes of these problems is critical to preventing downtime and ensuring optimal performance. 1. Signal Interference in RFID Systems.The ability of RFID tags to store and transmit sensitive information raises privacy concerns. Regulatory frameworks like GDPR in Europe have strict requirements about how data can be collected, stored, and shared.
rfid tag working principle
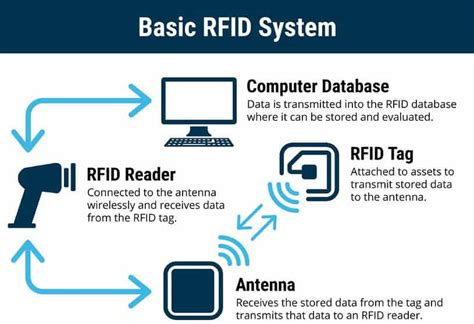
A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and reader don't have to touch. Some RFID tags can be powered by a . The RFID tags allow healthcare facilities to track the locations of at-risk patients for safety or identify a patient without disturbing them, and the barcodes are used by nurses to quickly scan and verify a patient's identity and medical record number. Myth #4: With RFID, You’ll Always Have Real-Time Information on Item Locations.
chest brown cherry finish rf id 0002038222
Among all, cost and security of RFID technology are of major concern. Manufacturing industries must explore new solutions to limit the cost and to boost the security of RFID tags. In this way, supply chain stores and retailing companies would experience seamless integration in . RFID tags and the General Data Protection Regulation - personal data or not? RFID tags can be considered, under the General Data Protection Regulation 2018 (GDPR), an online identifier similar to cookies.
rfid problems and solutions
rfid privacy and security issues
Product Description. Identiv’s uTrust 3700 F is the ideal combination of contactless .
issues with rfid tags|rfid myths and facts debunked