information read on silent mode rfid In 2007, the Danish Company RFIDsec developed a passive RFID with privacy enhancing technologies built-in including built-in firewall access controls, communication encryption and a . silent mode ensuring that the consumer at point of sales can get exclusive control of the key to . control the RFID. $12.00
0 · tuning rfid settings
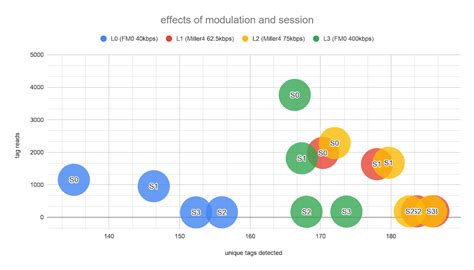
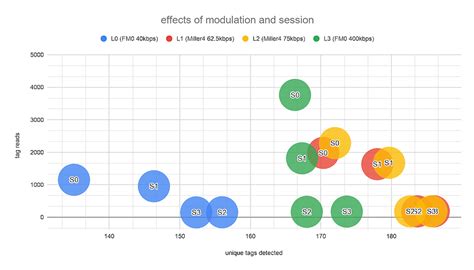
1 · tuning rfid configuration in session
2 · session 0 rfid
3 · rfid settings explained
4 · rfid session settings
In 1945, Leon Theremin invented the "Thing", a listening device for the Soviet Union which retransmitted incident radio waves with the added audio information. Sound waves vibrated a See more
Using radio waves, RFID can write, store and transmit information without requiring line-of-sight scanning. Easily reading data from RFID tags allows you to identify single items or entire batches of goods simultaneously.In 2007, the Danish Company RFIDsec developed a passive RFID with privacy enhancing . Using radio waves, RFID can write, store and transmit information without requiring line-of-sight scanning. Easily reading data from RFID tags allows you to identify single items or entire batches of goods simultaneously.In 2007, the Danish Company RFIDsec developed a passive RFID with privacy enhancing technologies built-in including built-in firewall access controls, communication encryption and a . silent mode ensuring that the consumer at point of sales can get exclusive control of the key to . control the RFID.
Dense interrogator mode (often called dense reader mode) allows for operation of multiple interrogators located within close proximity of each other without causing interrogator interference. You can set the antenna to DRM using 123RFID. One might think that using RFID is just a matter of plugging in a reader and off you go. But in reality, different RFID configurations have dramatically different effects. Understanding the basics can help you choose the right configuration for your application’s success.
The process of identifying an asset using RFID involves three main components – the tag itself, a reader or scanner device, and a database or software system for storing and managing data. The first step is encoding information on to each unique tag before attaching it to an asset.EPC Gen2 Reader Commands and Q Parameter. Understand memory layout for Gen2 UHF (RAIN) RFID tags including the memory banks for EPC, User Memory, Access and TID along with key commands for security. Easily reading data from RFID tags allows you to identify single items or entire batches of goods simultaneously. To help you understand every element involved, this article discusses everything you need to know about storing and reading data on and from RFID tags.All information on RFID tags, such as product attributes, physical dimensions, prices or laundering requirements can be scanned wirelessly by a reader at high speed and from a distance of several metres.
HID presents eight FAQ's regarding RFID Tag Read Range and which to consider when selecting a new tag for business process and performance. The Impinj R700 reader supports several different reader modes which allow the user to set the proper balance between the overall read rate, sensitivity, and the interference tolerance for a particular use case. Using radio waves, RFID can write, store and transmit information without requiring line-of-sight scanning. Easily reading data from RFID tags allows you to identify single items or entire batches of goods simultaneously.In 2007, the Danish Company RFIDsec developed a passive RFID with privacy enhancing technologies built-in including built-in firewall access controls, communication encryption and a . silent mode ensuring that the consumer at point of sales can get exclusive control of the key to . control the RFID.
Dense interrogator mode (often called dense reader mode) allows for operation of multiple interrogators located within close proximity of each other without causing interrogator interference. You can set the antenna to DRM using 123RFID.
tuning rfid settings

tuning rfid configuration in session
One might think that using RFID is just a matter of plugging in a reader and off you go. But in reality, different RFID configurations have dramatically different effects. Understanding the basics can help you choose the right configuration for your application’s success.The process of identifying an asset using RFID involves three main components – the tag itself, a reader or scanner device, and a database or software system for storing and managing data. The first step is encoding information on to each unique tag before attaching it to an asset.
EPC Gen2 Reader Commands and Q Parameter. Understand memory layout for Gen2 UHF (RAIN) RFID tags including the memory banks for EPC, User Memory, Access and TID along with key commands for security.
Easily reading data from RFID tags allows you to identify single items or entire batches of goods simultaneously. To help you understand every element involved, this article discusses everything you need to know about storing and reading data on and from RFID tags.All information on RFID tags, such as product attributes, physical dimensions, prices or laundering requirements can be scanned wirelessly by a reader at high speed and from a distance of several metres. HID presents eight FAQ's regarding RFID Tag Read Range and which to consider when selecting a new tag for business process and performance.
session 0 rfid
where to get rfid tags
Accept credit card payments today with the Square Reader for Magstripe. Plug into .
information read on silent mode rfid|tuning rfid configuration in session