rfid chips secuirty Identity thieves could read the same information from an RFID-enabled passport, or a security access card with an RFID chip. In 2006, a Dutch passport was read from ten . About this app. NFC Tag Reader & NFC Tools Writer is a simple and efficient application that lets you read contact-less tags on your smartphones and tablets. NFC Reader supports various tags like NDEF, RFID (Hi-band .
0 · where are rfid chips used
1 · types of rfid chips
2 · rfid chips in humans
3 · rfid chips for sale
4 · rfid chip pros and cons
5 · rfid chip meaning
6 · rfid chip manufacturing
7 · pros and cons of rfid
Blue Social is a free mobile app that introduces you to people in proximity. .
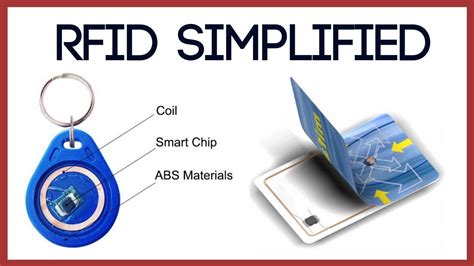
A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and .
RFID chips are a convenient way to store and access data, but they can also be vulnerable to malicious attacks. Hackers can use RFID scanners to steal money from your . A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and .
Identity thieves could read the same information from an RFID-enabled passport, or a security access card with an RFID chip. In 2006, a Dutch passport was read from ten .
Despite its widespread application and usage, RFID poses security threats and challenges that need to be addressed properly before deployment. This post aims to highlight several . An introduction to RFID security. 21 July 2023. This blog is intended for individuals with a technical background eager to explore Radio Frequency IDentification (RFID) . You probably know that the embedded computer chips found in most credit and debit cards are meant to protect you from financial fraud. But you may have also heard of a . The main security issue associated with the use of RFID systems is that they are susceptible to attacks or viruses from hackers and fraudsters. However, there is comfort in .
This bulletin provides an overview of RFID technologies and recommends practices for initiating, designing, implementing, and operating RFID systems in a manner that .Implementing robust security practices is crucial for safeguarding RFID systems against potential attacks. Here are some key best practices: Encrypt RFID Data: Encrypting the data .
This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world .
where are rfid chips used
types of rfid chips
hyundai nfc key card setup
RFID chips are a convenient way to store and access data, but they can also be vulnerable to malicious attacks. Hackers can use RFID scanners to steal money from your . A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and . Identity thieves could read the same information from an RFID-enabled passport, or a security access card with an RFID chip. In 2006, a Dutch passport was read from ten .
Despite its widespread application and usage, RFID poses security threats and challenges that need to be addressed properly before deployment. This post aims to highlight several . An introduction to RFID security. 21 July 2023. This blog is intended for individuals with a technical background eager to explore Radio Frequency IDentification (RFID) . You probably know that the embedded computer chips found in most credit and debit cards are meant to protect you from financial fraud. But you may have also heard of a .
The main security issue associated with the use of RFID systems is that they are susceptible to attacks or viruses from hackers and fraudsters. However, there is comfort in . This bulletin provides an overview of RFID technologies and recommends practices for initiating, designing, implementing, and operating RFID systems in a manner that .
Implementing robust security practices is crucial for safeguarding RFID systems against potential attacks. Here are some key best practices: Encrypt RFID Data: Encrypting the data .
clone nfc card to android
rfid chips in humans
The 2025 NFL playoffs are set to begin on Saturday, January 11th, and end with the Super Bowl on Sunday, February 9th. 2025 NFL Playoffs Key Dates. Jan 11-13: Wild-Card .
rfid chips secuirty|rfid chip manufacturing