rfid reader stealing Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking. For NFC payments to work, someone has to hold their mobile device or tap-to-pay card close to an NFC-enabled reader. The reader then uses NFC technology to search for and identify that payment device. Once it finds .
0 · what does rfid theft do
1 · rfid wallet scam
2 · rfid theft hack
3 · rfid theft
4 · rfid scam
5 · how to prevent rfid theft
6 · how do you steal rfid
7 · credit card rfid theft
Registered Partner - MIFARE: Contactless NFC Solutions | NXP Semiconductors
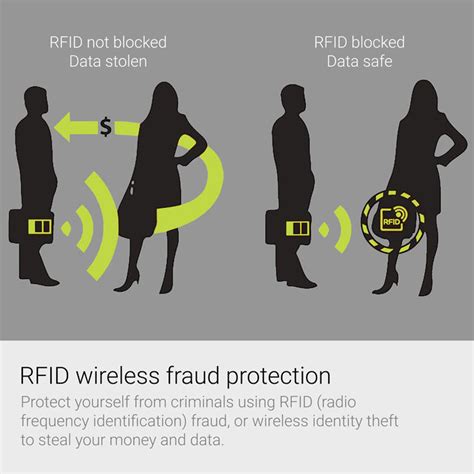
Some security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or personal information simply by walking within a few .
People often discover their credit card numbers have been stolen by receiving a transaction notification or bank statement showing an unfamiliar transaction. If your card is still with you, .
With some ingenuity and a cell phone bad actors can perform an RFID hack that will steal sensitive information or breach secured areas. Initially, experts stumbled upon this .
Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking. But as retailers speed ahead with RFID-enabled security strategies, consumer advocates raise concerns about how such tags could be used by retailers for marketing purposes without shopper.NFC/RFID skimming is where hackers/skimmers/bad guys intercept the radio wave communication between devices or simply read the radio waves that a NFC or RFID enabled . RFID scanners that capture and record ID information are certainly not legal, but for those with the proper skills, they’re easy to build. Hackers use a long-range reader to silently .
Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, . RFID theft, also known as skimming or electronic pickpocketing, involves the unauthorized access and theft of personal information stored on RFID-enabled cards or tags. .
RFID theft occurs when someone uses their own RFID reader to trigger the chip in your credit card; a process called ‘skimming’ or ‘digital pickpocketing.’ The card thinks it is being asked for information to carry out a sale. Some security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or personal information simply by walking within a few feet of you.People often discover their credit card numbers have been stolen by receiving a transaction notification or bank statement showing an unfamiliar transaction. If your card is still with you, it’s possible someone obtained your information while you were using the card or via an RFID reader.
With some ingenuity and a cell phone bad actors can perform an RFID hack that will steal sensitive information or breach secured areas. Initially, experts stumbled upon this technique while investigating the power emission levels in smart cards. Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking. But as retailers speed ahead with RFID-enabled security strategies, consumer advocates raise concerns about how such tags could be used by retailers for marketing purposes without shopper.NFC/RFID skimming is where hackers/skimmers/bad guys intercept the radio wave communication between devices or simply read the radio waves that a NFC or RFID enabled device puts out. The bad guy's reader reads the data put out from your device or debit/credit card.
smart flye card
RFID scanners that capture and record ID information are certainly not legal, but for those with the proper skills, they’re easy to build. Hackers use a long-range reader to silently steal this ID info from any RFID cards that happen to walk by.Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data.
RFID theft, also known as skimming or electronic pickpocketing, involves the unauthorized access and theft of personal information stored on RFID-enabled cards or tags. These cards and tags contain microchips that transmit data .
RFID theft occurs when someone uses their own RFID reader to trigger the chip in your credit card; a process called ‘skimming’ or ‘digital pickpocketing.’ The card thinks it is being asked for information to carry out a sale.
smart meter card
Some security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or personal information simply by walking within a few feet of you.People often discover their credit card numbers have been stolen by receiving a transaction notification or bank statement showing an unfamiliar transaction. If your card is still with you, it’s possible someone obtained your information while you were using the card or via an RFID reader. With some ingenuity and a cell phone bad actors can perform an RFID hack that will steal sensitive information or breach secured areas. Initially, experts stumbled upon this technique while investigating the power emission levels in smart cards. Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
But as retailers speed ahead with RFID-enabled security strategies, consumer advocates raise concerns about how such tags could be used by retailers for marketing purposes without shopper.NFC/RFID skimming is where hackers/skimmers/bad guys intercept the radio wave communication between devices or simply read the radio waves that a NFC or RFID enabled device puts out. The bad guy's reader reads the data put out from your device or debit/credit card. RFID scanners that capture and record ID information are certainly not legal, but for those with the proper skills, they’re easy to build. Hackers use a long-range reader to silently steal this ID info from any RFID cards that happen to walk by.Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data.
what does rfid theft do
rfid wallet scam
smart phone with 2 sim cards
The largest Selection of Digital Business Cards, Tags & More. All Tap Tags have .
rfid reader stealing|credit card rfid theft