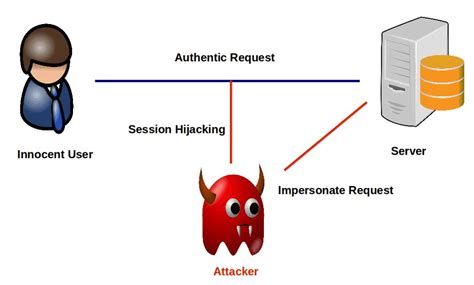
smart card session jacking The hacker gains access to a valid computer session key, and with that tiny bit of information, the intruder can do almost anything an authorized user can. We'll help you .
For me it’s mostly “If card number 53812736 is detected, go to this specific url” Reply reply . I’ve simply tested trying to read it through Shortcuts and NFC Tools since it won’t work normally. It .
0 · session hijacking software
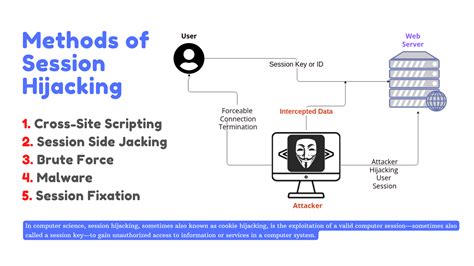
1 · session hijacking methods
2 · session hijacking link
3 · session hijacking examples
4 · session hijacking account
5 · ping session hijacking
6 · how to prevent session hijacking
7 · how does session hijacker work
$126.00
When an attacker takes over your internet session and controls your web activities, like while you’re checking your credit card balance, paying your bills, or online shopping, such . Session hijacking is a cyberattack whereby rogue actors gain access to a system or application when the victim is connecting online for a legitimate purpose. You could be logging . Bad actors looking to perform an account takeover attack may hijack an active user’s session. This “strategy,” often called session jacking, is a type of attack where an unauthorized party intercepts and steals an active . In a session hijacking attack, a hacker takes control of a user’s browsing session to gain access to their personal information and passwords. This article will explain what .
What is session hijacking? Session hijacking – sometimes called cookie hijacking, cookie side-jacking, or TCP session hijacking – occurs when an attacker takes over your internet session. .
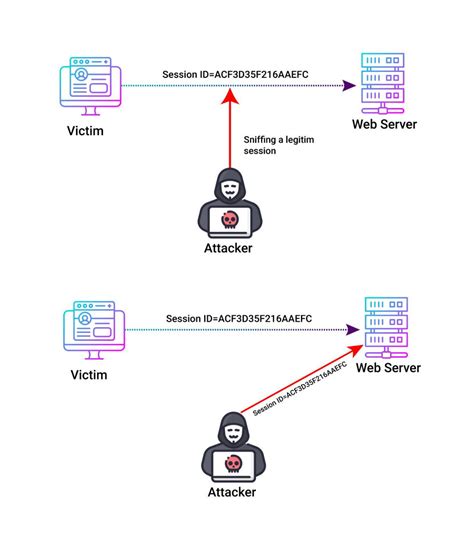
The hacker gains access to a valid computer session key, and with that tiny bit of information, the intruder can do almost anything an authorized user can. We'll help you . Session hijacking involves an attacker using captured, brute forced or reverse-engineered session IDs to seize control of a legitimate user’s session while that session is still . The attacker can now connect to any resource, on the same machine or on other machines, using the victim’s smart card and PIN number, effectively impersonating the victim’s .
A session hijacking attack happens when an attacker takes over your internet session — for instance, while you’re checking your credit card balance, paying your bills, or .
A session hijacking attack is one of the more common ways in which malicious actors can commit fraud. It allows black hat hackers to completely bypass secure . When an attacker takes over your internet session and controls your web activities, like while you’re checking your credit card balance, paying your bills, or online shopping, such . Session hijacking is a cyberattack whereby rogue actors gain access to a system or application when the victim is connecting online for a legitimate purpose. You could be logging . Bad actors looking to perform an account takeover attack may hijack an active user’s session. This “strategy,” often called session jacking, is a type of attack where an .
In a session hijacking attack, a hacker takes control of a user’s browsing session to gain access to their personal information and passwords. This article will explain what .What is session hijacking? Session hijacking – sometimes called cookie hijacking, cookie side-jacking, or TCP session hijacking – occurs when an attacker takes over your internet session. . The hacker gains access to a valid computer session key, and with that tiny bit of information, the intruder can do almost anything an authorized user can. We'll help you . Session hijacking involves an attacker using captured, brute forced or reverse-engineered session IDs to seize control of a legitimate user’s session while that session is still .
The attacker can now connect to any resource, on the same machine or on other machines, using the victim’s smart card and PIN number, effectively impersonating the victim’s .
session hijacking software
session hijacking methods
A session hijacking attack happens when an attacker takes over your internet session — for instance, while you’re checking your credit card balance, paying your bills, or .
A session hijacking attack is one of the more common ways in which malicious actors can commit fraud. It allows black hat hackers to completely bypass secure .
When an attacker takes over your internet session and controls your web activities, like while you’re checking your credit card balance, paying your bills, or online shopping, such .
Session hijacking is a cyberattack whereby rogue actors gain access to a system or application when the victim is connecting online for a legitimate purpose. You could be logging .
Bad actors looking to perform an account takeover attack may hijack an active user’s session. This “strategy,” often called session jacking, is a type of attack where an . In a session hijacking attack, a hacker takes control of a user’s browsing session to gain access to their personal information and passwords. This article will explain what .What is session hijacking? Session hijacking – sometimes called cookie hijacking, cookie side-jacking, or TCP session hijacking – occurs when an attacker takes over your internet session. . The hacker gains access to a valid computer session key, and with that tiny bit of information, the intruder can do almost anything an authorized user can. We'll help you .
Session hijacking involves an attacker using captured, brute forced or reverse-engineered session IDs to seize control of a legitimate user’s session while that session is still .
session hijacking link
session hijacking examples
$16.99
smart card session jacking|session hijacking methods