understand smart card authentication In its most simple form, public key authentication as follows: The server sends Alice a random string (nonce). Alice encrypts the nonce with her private key and sends it to the server along with her certificate. The Tiger 95.9 FM, the premier radio where music and sports update creates a lively radio listening experience. It’s an alternative music radio station based in Auburn, Alabama. Also. .
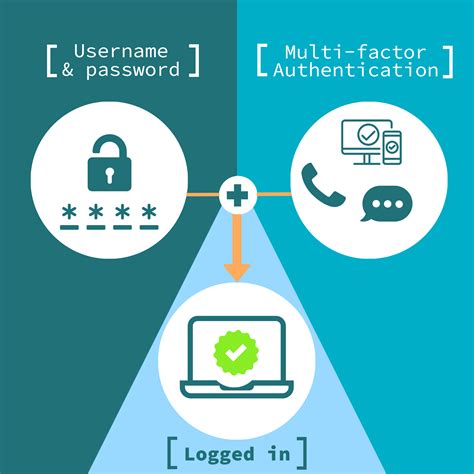
0 · smart card multi factor authentication
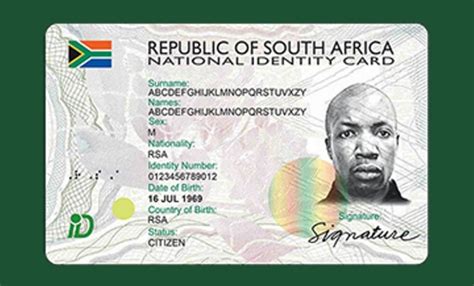
1 · smart card identity
2 · smart card based identification system
3 · smart card authentication step by
4 · smart card authentication protocol
5 · enable smart card log on
6 · enable smart card authentication
7 · authenticate using your smart card
ESPN 106.7. ESPN Auburn - Opelika, with the call-sign WGZZ-HD3, is a sports-format radio station serving Auburn and Opelika in Alabama. Its broadcast is also available globally via online live streaming, allowing people anywhere in the world to listen live to it.
smart card multi factor authentication
This section describes what a smart card is and how smart card authentication works. It .How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.
smart card identity
This section describes what a smart card is and how smart card authentication works. It describes the tools that you can use to read and manipulate smart card content. It also provides sample use cases and describes the setup of both the IdM server and IdM client for smart card authentication.
In its most simple form, public key authentication as follows: The server sends Alice a random string (nonce). Alice encrypts the nonce with her private key and sends it to the server along with her certificate.
Discover the benefits, challenges, and best practices for implementation. Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and .
Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.
Understanding Smart Card Authentication: Smart Card Authentication is how identity is checked using a smart card. The smart card has a microchip that can securely store and work with information. Comparing virtual smart cards with physical smart cards: compares properties, functional aspects, security, and cost. Authentication design options: describes how passwords, smart cards, and virtual smart cards can be used to reach authentication goals in .
Smart Card Authentication is a means of verifying users into enterprise resources using a physical card in tandem with a smart card reader and software.
smart card based identification system
A smart card is a secure microcontroller that is typically used for generating, storing and operating on cryptographic keys. Smart card authentication provides users with smart card devices for the purpose of authentication. Users connect their smart card to a host computer.The owner must physically have the smart card, and they must know the PIN to unlock it. This provides a higher degree of security than single-factor authentication (such as just using a password). In this page, we describe how to enable smart card authentication on Ubuntu. Note:How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.This section describes what a smart card is and how smart card authentication works. It describes the tools that you can use to read and manipulate smart card content. It also provides sample use cases and describes the setup of both the IdM server and IdM client for smart card authentication.
In its most simple form, public key authentication as follows: The server sends Alice a random string (nonce). Alice encrypts the nonce with her private key and sends it to the server along with her certificate. Discover the benefits, challenges, and best practices for implementation. Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and . Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.
Understanding Smart Card Authentication: Smart Card Authentication is how identity is checked using a smart card. The smart card has a microchip that can securely store and work with information.
Comparing virtual smart cards with physical smart cards: compares properties, functional aspects, security, and cost. Authentication design options: describes how passwords, smart cards, and virtual smart cards can be used to reach authentication goals in .
Smart Card Authentication is a means of verifying users into enterprise resources using a physical card in tandem with a smart card reader and software.A smart card is a secure microcontroller that is typically used for generating, storing and operating on cryptographic keys. Smart card authentication provides users with smart card devices for the purpose of authentication. Users connect their smart card to a host computer.
32 gb micro sd card for ld smart phone
smart card authentication step by
smart card authentication protocol
enable smart card log on
Elkhart County Radio Association Elkhart, Indiana. W9VMW Cass County Amateur Radio Club The Cass County Amateur Radio Club is a Non-Profit Organization serving Logansport, Indiana 46947. The CCARC participates in .
understand smart card authentication|smart card authentication step by